Expressvpn Glossary
Supply chain security
What is supply chain security?
Supply chain security is the practice of managing risks across the end-to-end lifecycle of products and services, including activities outside an organization’s direct control. In cybersecurity contexts, it covers selecting hardware, components, and services; integrating them into systems; operating them in production; and maintaining them over time, across internal teams and third parties.
The goal is to reduce the risk of tampering, fraud, compromise, or disruption, supporting trustworthy products and services.
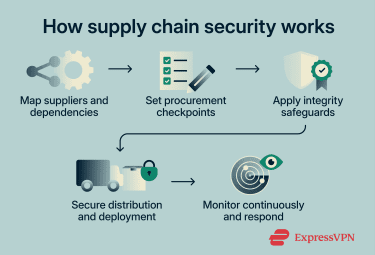
How does supply chain security work?
Supply chain security typically follows a general flow, with stages that include:
- Supplier and dependency mapping: Organizations identify the vendors, services, and components used to build, deliver, and operate products and services.
- Risk and criticality assessment: Dependencies are evaluated based on potential impact to operations, data, and system integrity; higher-risk items receive greater oversight.
- Requirements and accountability: Security expectations are established through procurement standards, contracts, and service agreements, including audit and notification terms.
- Control implementation: Controls are applied to reduce the risk of compromise and tampering, including strong authentication and access management, logging and monitoring, secure build and release practices, and integrity mechanisms such as code signing and Software Bill of Materials (SBOM).
- Ongoing monitoring and assurance: Organizations use continuous monitoring, testing, and risk-based supplier assurance activities to detect anomalies and validate that controls remain effective.
- Incident and disruption response: Response plans define how to contain affected components, remediate issues, maintain service continuity, and manage communications during supply chain incidents.
Types of supply chain security
Supply chain security has several sub-categories, which depend on sector and scope:
- Software supply chain security: Protects source code, dependencies, build systems, updates, and distribution channels from tampering or compromise.
- Hardware supply chain security: Addresses risks to hardware, firmware, and networking equipment during design, manufacture, assembly, and distribution.
- Logistics and physical supply chain security: Secures the manufacturing, movement, storage, and handling of physical goods to prevent theft, tampering, or disruption.
- Third-party vendor risk management: Manages risks introduced by external suppliers and service providers, including third-party access to internal systems, networks, and data.
- Digital service and information and communications technology supply chain security: Addresses risks involving cloud services, managed services, platforms, and data flows that support products and operations across suppliers and partners.
Where is supply chain security used?
Supply chain security is used anywhere products or services rely on external suppliers, components, logistics, or managed operations. In software delivery and continuous integration and continuous delivery (CI/CD), it helps manage risks from third-party code, build tools, and update mechanisms.
In cloud and managed services, it addresses exposure from service providers, shared platforms, and outsourced operations. In manufacturing and distribution, it reduces the risk of counterfeiting, tampering, and disruption as goods move through multiple parties.
It's especially important in sectors such as healthcare, finance, critical infrastructure, and commerce, where compromise or downtime can have high operational, regulatory, or customer impact.
Why is supply chain security important?
Supply chain security is important because it reduces the likelihood that third-party compromise, tampering, or disruption will affect products, services, and downstream customers.
A breach at a trusted or widely used supplier can affect many organizations, so supply chain controls help limit the scope and impact of incidents by improving visibility into dependencies, strengthening detection and containment, and supporting resilience if a supplier fails or is compromised.
It also supports compliance and procurement requirements by establishing clear security expectations for suppliers and service providers. Response planning improves operational continuity by enabling faster isolation, remediation, and recovery during supply chain incidents, helping maintain reliable services and protect sensitive data.
Risks and privacy concerns
Supply chain security reduces risk, but large, multi-tier supply chains limit visibility beyond direct vendors, especially into subcontractors. This can hide weak access controls, insecure data handling, or inadequate incident response, increasing privacy exposure when suppliers access sensitive data without effective oversight and monitoring.
Compromised upstream parties can introduce counterfeit components, tampered updates, or vulnerable dependencies that propagate across downstream connected systems. Foreign ownership, control, or jurisdiction can also create legal and political risk that affects data handling and service continuity.
Further reading
- Cybersecurity lessons: Risk of email takeover via a 4th-party provider
- Log4Shell vulnerability: What it is and how to stay protected
- Log4Shell’s long-tail impact on your security
FAQ
What’s the difference between vendor risk and supply chain security?
How do supply chain attacks usually happen?
Another common pattern involves dependency mix-ups in package ecosystems. This can include private vs. public package name collisions (often called dependency confusion), where automated tooling pulls an unintended public package that shares a name with an internal one, as well as typosquatting, where look-alike or mistyped package names lead to the wrong package being installed. In both cases, the core issue is that routine dependency resolution and installation processes bring untrusted code into the environment.

