Expressvpn Glossary
Direct memory access (DMA)
What is direct memory access (DMA)?
DMA is a feature that allows some hardware devices to read from or write to a system’s memory directly, without the CPU managing every step.
Normally, in computer systems, the CPU controls when and how data is moved between hardware and memory. DMA is intended to free up the CPU for other tasks, improving overall system efficiency.
How does DMA work?
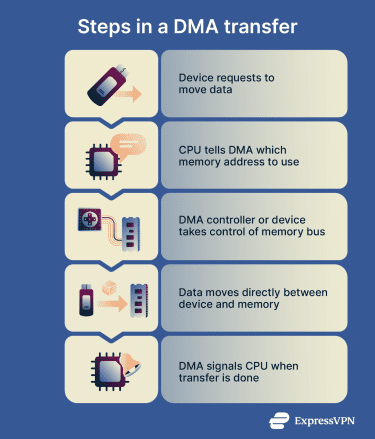
A DMA transfer follows a set of steps whenever data needs to be transferred directly to or from memory.
- Device signals intent: The device indicates that it wants to move data.
- CPU setup: The CPU prepares for the transfer by specifying which memory locations to use and how much data to move. For more complex transfers, this information may be organized into “descriptors.” Multiple descriptors can be combined into a “scatter-gather list” to move data from multiple memory locations in a single operation.
- Hand-off to DMA controller or bus master: The CPU passes the task to a DMA controller, a hardware component that coordinates access to the memory bus (the physical pathway data uses to travel between memory and devices). Alternatively, some devices support bus mastering, which lets them take control of the memory bus and handle the transfer themselves without a DMA controller.
- Data transfer: The DMA controller or bus-mastering device moves data directly between the device and memory.
- Completion notification: Once the transfer is finished, the DMA controller or bus-mastering device sends an interrupt, a signal to the CPU indicating that the transfer is complete. The CPU can then take any necessary follow-up actions, such as processing the transferred data or marking the transfer as complete for software to use.
Why is DMA important?
By allowing data to move between devices and memory with less CPU involvement, DMA:
- Reduces CPU workload: Since the CPU doesn’t need to manage data transfers actively, it’s free to handle other tasks.
- Speeds up transfers: Disk, network, and peripheral data can reach their destinations faster because DMA cuts out the middleman.
- Improves overall system performance: With DMA, the CPU is no longer a potential transfer bottleneck, increasing throughput.
These benefits make DMA critical for real-time and streaming applications, for example, audio/video pipelines or embedded systems, where data must arrive continuously and on time.
Where is DMA used?
DMA is implemented in many types of input/output (I/O) hardware, including:
- Network cards and Wi‑Fi adapters: Move network packets directly to and from memory, improving overall network performance.
- Storage devices (NVMe, SATA, RAID): Transfer blocks of data between memory and drives quickly, speeding up file access and data transfers.
- GPUs and accelerators: Move graphics or compute data without stalling the CPU, supporting fast rendering and parallel computations.
- USB controllers and peripherals: Enable efficient transfers for USB devices, from storage drives to other connected hardware.
- Audio interfaces and cameras: Handle continuous audio or video streams reliably, avoiding delays or interruptions.
Risks and privacy concerns
While DMA can improve performance, its capabilities can also create privacy and security risks if it's not properly controlled. This is because DMA lets devices bypass normal CPU checks.
As a result, a malicious or compromised device might be able to read or change parts of memory that are normally protected. That can include sensitive data like passwords, encryption keys, or active sessions.
High-speed, hot-pluggable interfaces like Thunderbolt or USB-C create an additional risk. Devices connected through these ports can gain DMA access as soon as they’re plugged in, which means a rogue device could potentially exploit that access to read or modify memory.
Systems try to guard against these risks through mechanisms like the I/O Memory Management Unit (IOMMU), which controls the parts of memory a device can access. But in situations where IOMMU is absent, misconfigured, or not yet active, sensitive data could be exposed.

