-
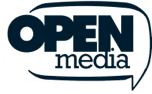
The AI era requires a new way to control your VPN. So we built it.
ExpressVPN is the first VPN provider to adopt the Model Context Protocol (MCP). We built a strictly local bridge that lets your AI coding assistants manage your network routing without ever opening a ...
-
How to perform a factory reset on your Oculus Quest
Common Oculus Quest issues, like buggy apps, slow performance, connectivity issues, or freezes, are often easy to fix. However, if these issues persist, a factory reset may help. This guide explains h...
-
What is HTTP/3 and should you use it?
HTTP/3 is the newest version of Hypertext Transfer Protocol (HTTP), the protocol that allows browsers to request web pages and servers to send them back. It defines how those requests and responses ar...
-
How to make your X account private: A comprehensive guide
X (formerly Twitter) lets you control who can see and interact with your posts. It adds a layer of privacy and security while still allowing you to post, read, share, and comment as usual. People can ...
-
Most secure Linux distro: Best picks by threat model
Choosing the most secure Linux distro is about matching the system to its intended use, the sensitivity of the data it handles, and the level of setup and ongoing maintenance that are realistic. In ma...
-
How to delete your Tumblr account: Fast desktop and app walkthrough
Whether you're stepping back from social media, tidying up your digital footprint, or simply finished with the platform, deleting your Tumblr account takes just a few minutes. This quick guide shows t...
-
How we engineered a way to restrict child sexual abuse material without looking at your data
Our new partnership with the Internet Watch Foundation (IWF) proves that strong encryption and targeted CSAM prevention can coexist through careful DNS engineering. For years, the fundamental operatin...
-

How to clear cache on Xbox for better performance
If your Xbox is experiencing performance drops, delayed load times, update errors, or interface slowdowns, clearing the system cache can help. Temporary system data occasionally becomes corrupted or i...
-
What is home title theft (deed fraud)? How to spot it and protect your home
Home title theft, also known as deed fraud (or title fraud), is a scam in which someone files fraudulent property documents to make it appear that they own the property. It often doesn’t require mov...
-
How to clear cache in Firefox on desktop and mobile
As Firefox is used to browse the web, it stores temporary site resources over time. In some cases, these stored files become outdated, which can contribute to slow loading, display glitches, or older ...
Featured