Virtual kidnapping: How it works and how to protect yourself
Virtual kidnapping is a type of phone scam in which criminals falsely claim to have kidnapped a person’s child or another loved one and demand immediate payment to prevent harm. The call may include a distressed voice in the background or someone claiming to be the victim, creating a sense of urgency intended to pressure the target into acting quickly.
No one is actually abducted in a virtual kidnapping. Instead, scammers rely on fear, time pressure, and limited information to make the threat seem credible. In some cases, they may also use AI voice cloning tools to imitate familiar voices, making these calls appear more convincing.
This guide explains how virtual kidnapping scams work, who scammers typically target, common warning signs, and steps that can help people respond safely if they encounter this type of fraud.
What is virtual kidnapping?
Virtual kidnapping is a phone extortion scam in which someone calls and falsely claims they have abducted someone you love. It’s a form of phone-based fraud where criminals manipulate victims over the phone to make them pay a ransom.
Unlike a real kidnapping, there’s no physical crime in progress. The scammer’s only tool is the phone call itself. If you pause and verify the situation, it often becomes easier to identify the call as a scam. That’s why these scams rely heavily on urgency and emotional pressure.
Most virtual kidnapping calls share the same core features, no matter how they’re framed:
- Urgency: A deadline that forces you to act in minutes, not hours.
- Fear: Threats of violence or harm if you hesitate or hang up.
- Isolation: Instructions not to contact anyone else or the authorities.
- Unrecoverable payment: Demands for wire transfers, gift cards, or cryptocurrency.
How does a virtual kidnapping scam work?
Most of these scams follow the same basic pattern. The caller moves fast because time is their biggest advantage. The longer you have to think, the more likely you are to see through it.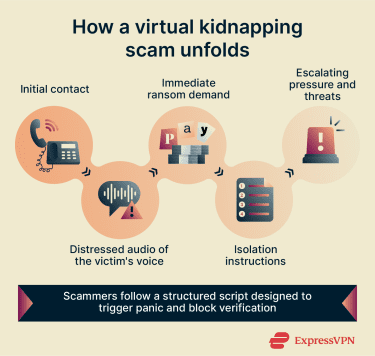
Here’s how a typical call unfolds:
- The call opens with a distressed voice: The target hears what sounds like their loved one crying, screaming, or calling their name. In some cases, this is a real person playing a role. In others, it’s AI-generated audio built from voice clips the scammer found online.
- A second voice takes control: The “kidnapper” comes on the line and makes the demand. They often use personal details they’ve collected in advance, like names, locations, and past and recent events, to make the situation feel real.
- They demand payment immediately: Wire transfers, cryptocurrency, payment apps, and gift cards are the most common requests. These methods make it hard or impossible to reverse the payment once it’s been sent.
- The target is told not to hang up: The caller warns the target that ending the call will put their loved one in danger. This is a key tactic: keeping the victim on the line prevents them from calling the real person to check if they’re safe.
- Pressure keeps building: Deadlines get shorter, threats escalate, and the ransom amount may drop quickly if you hesitate, which is another sign that the caller simply wants payment before you catch on.
Virtual kidnapping scams can also start with text messages, where scammers send the victim AI-altered photos or videos of their loved ones as fake “proof of life.” On closer inspection, these images often contain errors such as wrong body proportions, missing tattoos, or blurred facial details. That said, AI image-generation tools are improving rapidly, so it may not always be possible to identify a fake image through visual inspection alone.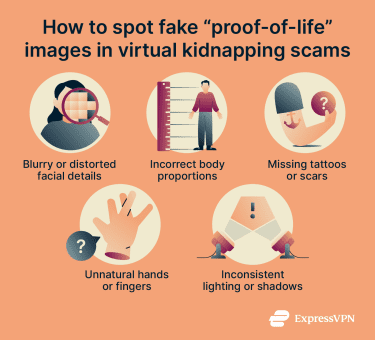
How scammers find their targets
The more a scammer knows about their target, the more convincing the call sounds. The more personal the story feels, the harder it is for someone to dismiss the call as a random scam. That’s why many virtual kidnapping attempts start with research. And most of the information they need is sitting in plain sight on the internet.
They typically look for:
- Public social media posts: Updates about travel, school schedules, family events, or daily routines reveal names, relationships, and locations. Even something small, such as a parent tagging their child in a photo, can give a scammer enough to work with.
- Real-time travel announcements: Posting about flights, vacations, or business trips signals to a scammer that someone in your family may be hard to reach. That gap is exactly what they need to make their story sound plausible.
- Public audio and video: Voice cloning tools may be able to replicate someone’s voice using even short audio samples. Publicly posted videos of children or other family members can provide that material without the subject ever knowing.
- Data breach records: Phone numbers and email addresses exposed in company data leaks can end up for sale online, giving scammers a ready-to-use contact list. Tools such as ExpressVPN’s ID Alerts, available for eligible U.S. subscribers, can notify you if your personal information appears in known data breaches.
Who is most at risk?
Anyone can receive a virtual kidnapping call. Scammers sometimes work through lists of numbers without knowing much about the person on the other end.
However, targeted versions, where the caller has done research and knows names, relationships, and schedules, may focus on specific groups based on two factors: emotional vulnerability and difficulty verifying the situation quickly.
- Parents and grandparents: Calls involving a child in danger trigger a fast emotional response. The harder it is to think clearly, the better the scam works.
- Families of international travelers: When a loved one is in a different time zone or country, it takes longer to confirm they’re safe. That delay is valuable to the scammer and makes the story seem more plausible.
- Older adults: Scammers often assume older people are more likely to respond to an urgent phone call without questioning it, especially if caller ID spoofing makes the number look familiar.
- Executives and public-facing professionals: People with a visible online presence have more personal information available, which makes it easier for a caller to personalize a fake scenario and make it sound specific.
Scammers also tend to time their calls strategically: during school hours, late at night, or when they know from social media that a family member is traveling. The harder the target would find it to reach the “victim,” the more the situation plays into their hands.
What to do if you get a virtual kidnapping ransom call
Receiving a call claiming that someone you love has been kidnapped is a terrifying experience in itself and can involve a real emergency. But criminals also use this tactic in virtual kidnapping, where no one has actually been abducted. Simply being aware that these scams exist and knowing their red flags can help you pause and verify what’s really happening.
Below, we summarize questions you can ask to help determine whether the call may be real, based on guidance from the FBI. We also outline what to do if you later realize the call was a scam and how to report it.
Questions to verify whether a call is real
If you receive a call claiming that a loved one has been kidnapped, the FBI recommends asking questions and taking steps that can help verify whether the situation is real.
According to the FBI’s guidance on virtual kidnapping scams, you can try the following:
- Ask to speak directly to the alleged victim: For example, ask: “How do I know my loved one is okay?” Or request that the victim call you back from their own phone.
- Ask questions only the victim would know: This can be personal details or recent events.
- Ask the caller to describe the victim: Ask them to provide specific information about them.
- Call the supposed victim from another phone: If the caller insists that you stay on the line with them (a common scam tactic), try to contact the person through another phone or other channels, such as text messages or social media.
- Attempt to confirm the victim’s location if possible: If you know where the person was supposed to be (such as at work, school, or traveling), try contacting those locations or people nearby who may be able to confirm their safety.
The FBI also advises staying calm, avoiding sharing personal information during the call, and trying to buy time if possible. If you’re unsure whether the situation is a virtual or real kidnapping, you should contact local emergency services or the nearest FBI office.
How to report a virtual kidnapping event
Report the call even if you didn’t lose any money. These reports help law enforcement identify patterns and connect cases.
- In the U.S.: File a report with the FBI’s Internet Crime Complaint Center (IC3) at ic3.gov or with the Federal Trade Commission (FTC) at reportfraud.ftc.gov.
- In the U.K.: Contact Action Fraud at actionfraud.police.uk.
- In Canada: Report to the Canadian Anti-Fraud Centre at reportcyberandfraud.canada.ca/.
After reporting the incident, take time to review what information is publicly available about you and your family online.
Check social media privacy settings, remove relationship labels where possible, and consider whether any recent posts revealed travel plans or schedules. You don't need to overhaul your digital life (although you can if you wish to); a few targeted changes can meaningfully reduce what a scammer could find.
If you did share financial information or send money, contact your bank immediately. Also, update passwords on any accounts where you may have revealed login details during the call.
Tip: To quickly replace your passwords on affected accounts with strong and unique ones, consider using a password manager such as ExpressKeys.
How to reduce your risk of a virtual kidnapping scam
You can make the scam harder to pull off by limiting what strangers can learn about you and your family online and by having a simple plan ready in advance.
Reduce your public profile
- Set social media accounts to private: Review who can see your connections list. Public follower lists reveal family relationships that scammers can exploit.
- Don’t post travel plans in real time: Wait until you’re home before sharing holiday photos or check-ins.
- Remove relationship labels from public profiles: Platforms that let you tag family members give scammers a ready-made diagram of who matters to you most.
- Be careful with public audio and video: As mentioned, voice cloning tools need just a few seconds of audio. If you regularly post videos of yourself or your children speaking, make those posts visible to friends only.
Agree on a family code word
A shared code word or phrase is one of the most practical defenses against this scam. It shouldn’t be something visible on social media, such as a birthday or a pet’s name, and should be easy to remember under pressure.
Talk to the people most likely to be targeted
For older relatives, explain that scammers can now spoof caller ID to make calls appear to come from a known number and that AI can imitate a familiar voice. Agree on a simple rule: if they ever get an urgent call asking for money, they hang up and call you back on a number they already have saved. Don’t call back the number that just called.
For teenagers and students, talk them through what a cyber kidnapping scenario looks like: someone posing as an authority figure, creating fear, and telling them to isolate and not contact their family.
Make it clear that no legitimate authority would demand that someone disappear and stop answering calls. If they ever get a call like this, they should contact a trusted adult immediately.
Having this conversation before it happens matters. When you're in a state of fear, you're much less likely to think clearly. Knowing the playbook in advance gives everyone a better chance of responding calmly.
Learn more: For additional cybersecurity guidance tailored to different age groups, see our guides on online safety for seniors and internet safety for kids.
Check your digital exposure
Start by looking up your own information. Search your name and your family members' names online and see what comes up. If your phone number, address, or workplace appears in public results, consider what a scammer could do with it.
You should also monitor data breach exposure. Services like ExpressVPN’s Identity Defender (available to select U.S. users) can alert you if your personal data has appeared in a known data breach. If it has, update your passwords and enable two-factor authentication (2FA) on key accounts.
FAQ: Common questions about virtual kidnapping
How can I recognize a virtual kidnapping scam?
How do scammers get my information?
What is a family code word, and does it actually work?
How do I report it, and is it worth reporting if I didn’t lose any money?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN